A few months ago I started building out a home lab focused on detection engineering. This project covers Linux SIEM monitoring with Splunk and OpenSCAP on a hardened Ubuntu 24.04 VM with detections mapped to MITRE ATT&CK.
The starting point is OpenSCAP, an open source tool that evaluates a system against a security benchmark and generates a pass/fail report for each control. The benchmark I used is the Ubuntu 24.04 STIG V1R1, a hardening standard published by the Defense Information Systems Agency. A fresh install scored 50.48%. After running auto-remediation and manually fixing the firewall and time synchronization controls, the score reached 78.39%.
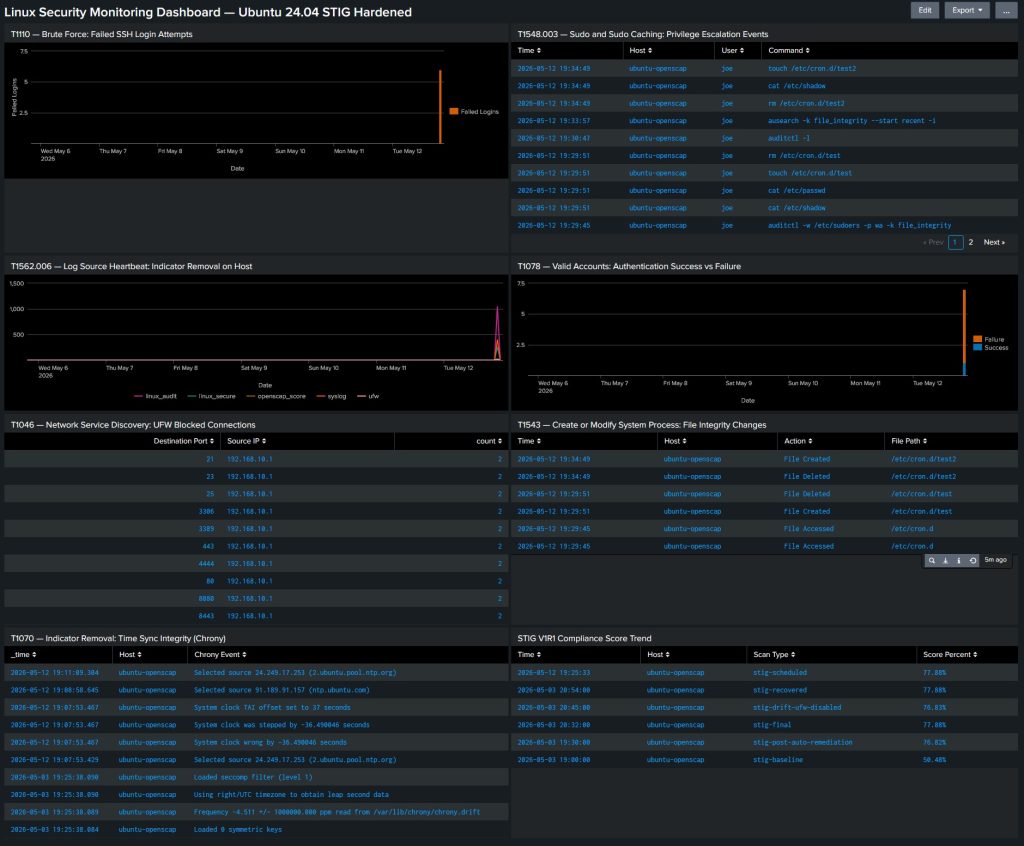
From there I configured a Splunk Universal Forwarder to ship four log sources into a dedicated index: authentication logs, kernel audit events, syslog, and UFW firewall logs. An eight-panel dashboard maps that telemetry to ATT&CK techniques. One thing that took some work was getting auditd file integrity events to surface correctly. Linux auditd writes SYSCALL and PATH records as separate linked entries, so getting the actual file path to show up in Splunk required understanding how those records relate to each other rather than just writing a regex and hoping for the best.
I also simulated configuration drift by disabling the firewall and adding a suspicious cron job. The compliance score dropped and both events appeared in the dashboard before a scheduled scan would have caught them. A cron job now runs OpenSCAP daily and logs the score automatically.
The full write-up for this Linux SIEM monitoring project with Splunk and OpenSCAP is available on GitHub, including the dashboard XML, forwarder configuration, auditd rules, and the automated scan script.