A couple weeks ago I installed an intrusion detection system, Suricata, on my home network to see if anything interesting showed up through Splunk. Now, my goal isn’t to monitor every single website that my family uses. Rather, see if the host devices are doing anything that they should not be doing.
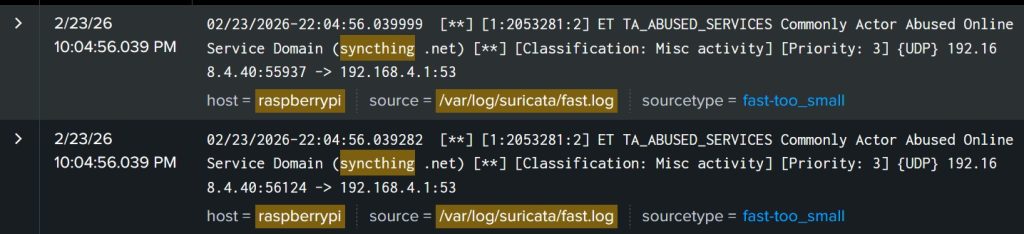
I started off slow and installed the Emerging Threats rule-set. So far, it’s pretty boring. Some standard DNS lookups. It really did not like that I use Syncthing 𝘌𝘛 𝘛𝘈_𝘈𝘉𝘜𝘚𝘌𝘋_𝘚𝘌𝘙𝘝𝘐𝘊𝘌𝘚 𝘊𝘰𝘮𝘮𝘰𝘯𝘭𝘺 𝘈𝘤𝘵𝘰𝘳 𝘈𝘣𝘶𝘴𝘦𝘥 𝘖𝘯𝘭𝘪𝘯𝘦 𝘚𝘦𝘳𝘷𝘪𝘤𝘦 𝘋𝘰𝘮𝘢𝘪𝘯 (𝘴𝘺𝘯𝘤𝘵𝘩𝘪𝘯𝘨 .𝘯𝘦𝘵). Although, it is understandable why that would be an alert for a corporate environment.
My favorite command has been 𝘴𝘶𝘥𝘰 𝘴𝘦𝘥 -𝘪 '/𝘓𝘪𝘯𝘦 𝘵𝘰 𝘙𝘦𝘮𝘰𝘷𝘦/𝘴/^/#/' 𝘧𝘪𝘭𝘦_𝘯𝘢𝘮𝘦.𝘳𝘶𝘭𝘦𝘴 to add a # to comment out a line in a rules file. (Don’t copy paste commands unless you know what you are doing).
Next is to activate some more interesting rulesets and see if I have a C2 server hiding somewhere.